 Posted by VinciWorks
Posted by VinciWorks
Recently there has been a lot of buzz in the public sphere surrounding data protection, information security and cyber security. The EU is toiling along with its reforms to the Data Protection Regulation; Lexcel added an information security training requirement to the new Lexcel V6; and the Home Office has launched a cyber security awareness campaign.
The ubiquity of these terms in the industry — along with some actual overlap in meaning — has led to confusion about their definitions and misuse of the terms.
Information security and cyber security
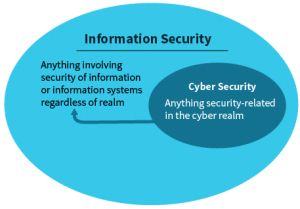
These terms are often misused, because they are nearly synonymous. Both information security and cyber security are defined as the practice of defending information from unauthorised access, use, modification or disruption. The only difference between the two disciplines is in the form of the data. While cyber security refers only to electronic security, information security is a broader term that encompasses all data, both physical and digital.
Training requirements
The requirement to train on information security is derived from outcome 4.1 of the SRA handbook. Additionally section 3.1(i) of Lexcel requires “training for personnel on information security.”
To fulfil this requirement, we recommend in-depth training on information security for all staff during on boarding and refresher training every 24 months. General information security courses include both information security and cyber security in one course.
Data protection
Data protection is a set of laws, regulations and best practice directing the collection and use of personal data about individuals. Data protection differs from information security in two fundamental ways. One, it only encompasses personal data. Two, due to the sensitive nature of personal data and the public’s expectation of privacy, various requirements are imposed, above and beyond the base requirements of information security.
For example, in the UK the use of information about individuals is regulated by the Data Protection Act 1998 and is in line with the EU’s Data Protection Directive.
The act distinguishes between ‘personal data’ and ‘sensitive personal data’ (such as ethnic background, religious beliefs, health etc.). It provides rules on how the data may be stored, transferred across borders, and used in business activities (e.g. for marketing). It also stipulates how long you can retain personal data that is not actively in use.
An interesting note is that any information that is not identifiable as belonging to a particular person, no matter how confidential it may be, is not subject to the Data Protection Act.
Training requirements
Outcome 7.5 of the SRA handbook states that you must “comply with legislation applicable to your business, including anti-money laundering and data protection legislation”.
To fulfil this requirement, we recommend in-depth training on data protection for all staff during onboarding.